
DevTest Lab is a self-service sandbox environment to quickly create dev/test environment.
- Create once, use everywhere, by everyone.
- Quickly ready for testing.
- Start with Azure Market base images or your own VHD.
- Worry-free self-service and controlling costs.
- Automate environment provisioning.
- Integratable with existing toolchain.
There is some companies, which have used it already with their own configuration. We can read about the customer’s experience with Azure DevTest Labs on the Microsoft Customer Stories Webpage.

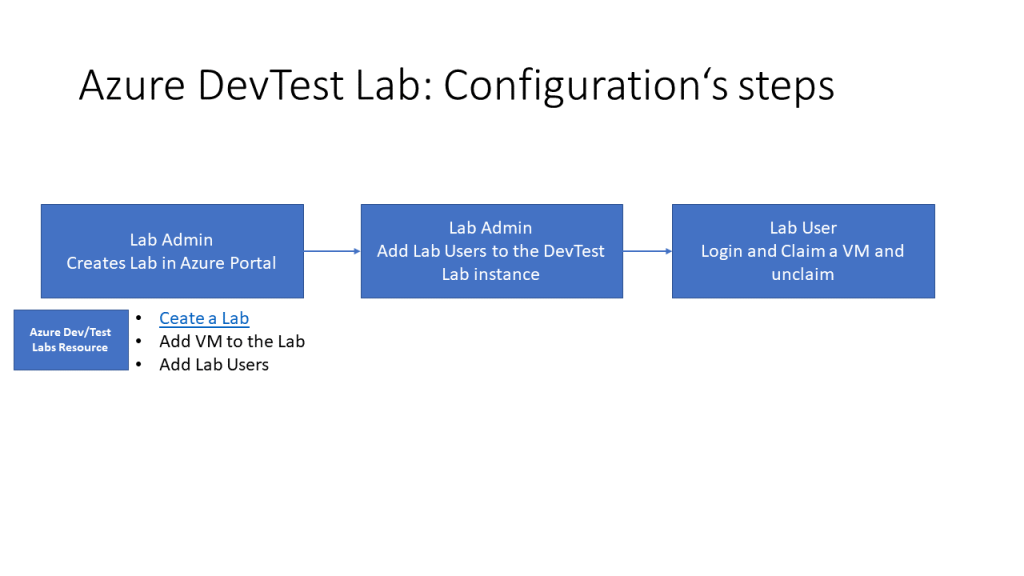

How to start with Dev/Test Lab:
It’s possible to start with server configuration and configure a user to be a dev/Test user.
*** This is the picture of the server configuration
To solve the pain points of the projects, which are working with VMs and configure the development and test environment and apply the customized policies. This solution must be able to solve the following issues:
- Manage security, identity,
At the Enterprise level it must be purchasable like an entity.
the Dev/test is not with the access policy of user under azure subscription dependent but even a user/ viewer user can create an instance/environment and configure the environment.
we must consider the subscription limitation because the provisioning will be reduced from the subscription resource.
They have an orchestrator for the user and new onboarding and it’s DevOps. The configuration of the DevTest machines can be done with Azure DevOps Artifacts. It’s very flexible customizable. Therefore the softwares can be installed in initialization time.
the whole solution is template based and all can be customized and even ARM can be used for architecture configuration and even infrastructure. and even the compliance gate process can be a part of the ARM context.
How we can automate this process for new updates from Microsoft?
the best fault check and confirmation must be editable via all but only confirmable via pull request. But a person in each person in a team can edit the arm.
ADD and Azure DevOps have their own user center and therefore the user must be inserted in Azure DevOPs.
And all this steps are managed with an orchestrator and this is only an Azure Function.
App Center can be a better steps for managing the Mobile App.
The enterprise use it oft for external users because they have different configured machines.
The configurations are like as follows:
- All the Vms in DevTest are on a same VNet but -> vnet peering -> ExpressRoute
- on-prem datacenter are accessable via APIM or data example as dommy in template and on VMs in DevTest
Paas are not good idea for enterprise but they prefer the Iaas an Saas. The outside -> 443+https -> GW+Function for generate token ->3398 -> Vm in DevTest
we can manage the devtest with two different users. Manage/admin & user. For managing the images and usage the images and then the timespan in which the machine must be able to be up and run.
consider terraform azure later in text
Reference
